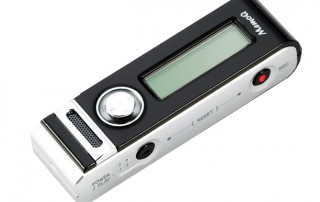
Cameras and surveillance devices end up in the darndest places.
A spy camera was found in a meeting room in the National Palace, President López Obrador revealed Thursday morning.
During a daily news briefing Lopez Obrador said the device had been found in a meeting room in the National Palace, his headquarters.
“A few days ago, in one of the rooms in our offices, a sophisticated camera was found, one of those little-bitty ones, they were recording us,” he said in his morning address. “In a room here in the palace, not in my office, but one of the rooms where we have meetings.”
“He who owes nothing fears nothing,” said the president, who says he was not troubled by the discovery.

President Andres Manuel Lopez Obrador, holds a tiny camera he says was being used to spy on his meetings, during his morning news conference […]